5 Key Takeaways from the Datto SMB Cybersecurity for MSPs Report
The Datto SMB Cybersecurity Survey for MSPs Report is packed with crucial information for MSPs to help them grow their sales and learn more about their clients’ pain points. The survey was created from a subset of data collected in a survey of 2,913 IT decision-makers conducted in July and August 2022. Respondents were required to be an IT decision-maker at an SMB with 10–300 employees. The markets chosen for analysis were North America (U.S. and Canada), the U.K., Germany, Australia and New Zealand, the Netherlands and Singapore. In addition, we sat down with two Kaseya experts, Chris McKie, VP of Product Marketing Security and Networking Solutions and Mike DePalma, VP of Business Development, to get their expert insights into this year’s trends.
Our 5 Key Takeaways from the Datto SMB Cybersecurity for SMBs Report
Businesses are getting the message that cybersecurity is critical to their success loud and clear, and they’re acting accordingly, creating a world of opportunity for MSPs. However, there are still some challenges for MSPs to face in overcoming customer objections and reinforcing the fact that security is a smart investment. These are five of the most notable data points in our report for MSPs:
1. IT decision-makers are in a buying mood.
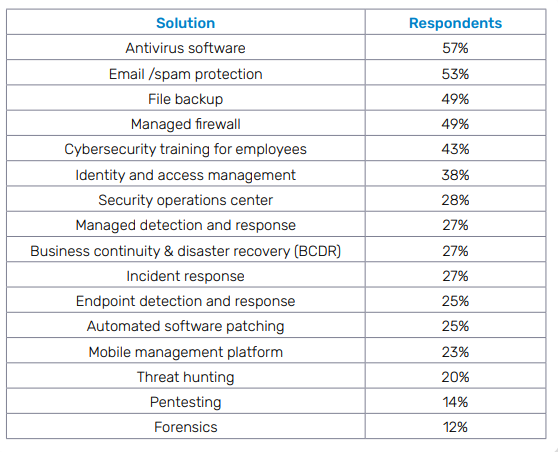
Businesses are very concerned about security and ready to make investments to keep their organizations safe. SMBs understand that with cybercriminals finding new ways to attack their data, they need help protecting their valuable data. About half of our survey respondents plan to spend on email security, backup and antivirus protection (see Figure 1).
Some SMB security shopping will revolve around the challenges that businesses face to maintain compliance with cyber insurance requirements, or even get cyber insurance at all. As Chris McKie points out, the required solutions to comply with insurance company security mandates can be a great sales conversation starter.
“Looking at it from a cyber insurance requirements perspective, EDR is often mandated,” said McKie. “We’re also seeing more and more of managed SOC or managed detection and response (MDR) as a mandated item. Security awareness training is also one of those check box items with many insurers.”
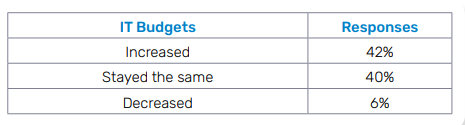
2. Security is front and center on most SMB priority lists.
High-profile cyberattacks and strict data privacy laws have increased the importance of security for businesses. Four in 10 of our survey respondents said that their organization is increasing their cybersecurity spending, and most expect that to continue –— excellent news for MSPs in today’s challenging economy (see Figure 2).
One way that MSPs can help direct that spending is by conducting tabletop exercises that simulate cyberattacks with their clients. That brings what a client might need when the worst happens into perspective, proving the value of some security tools.
“It’s so important to conduct tabletop exercises,” advises McKie. “It is a way that an MSP can go in, meet with the business owners and conduct a make-believe scenario like what happens if you get hit with ransomware? Having these exercises on a regular basis further instills the MSP as a subject matter expert and it shows where the client’s gaps are.”
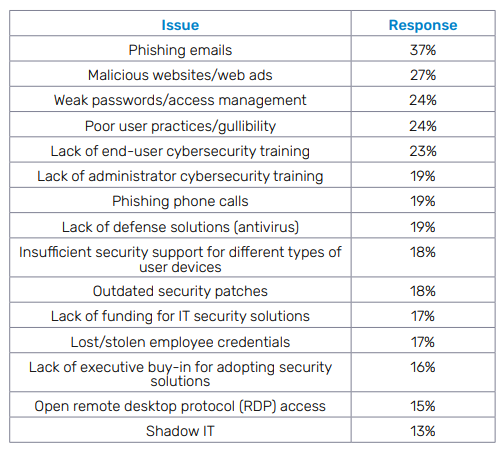
3. Phishing is the biggest security woe that SMBs face.
Business IT leaders are worried about phishing and the danger it brings in its wake. Malicious advertisements are also troubling businesses. It’s interesting to note the prominence of poor security practices and lack of training on this list. Security awareness training is a powerful and affordable tool for any business to use to mitigate security risk, yet far too many businesses aren’t getting the full benefit due to running haphazard or infrequent training. This list does contain a spot of good news for MSPs: there are revenue growth possibilities for MSPs around email security and security training with phishing simulations (see Figure 3).
Even though everyone seems to know about phishing and knows that it is dangerous, bad actors still rely on phishing to launch many dangerous cyberattacks like ransomware and business email compromise (BEC). Why? Because phishing is cheap and highly effective. Cybercriminals don’t even have to do the phishing themselves thanks to Phishing-as-a-Service practitioners on the dark web. This problem won’t be going away anytime soon.
“The delivery system for cyberattacks hasn’t changed that much because they don’t have to change it,” said DePalma. “Cybercriminals know that the same delivery system they’ve been using, a phishing email, is working.”
4. Downtime is costly, but many businesses don’t have the right tools in place to minimize it.
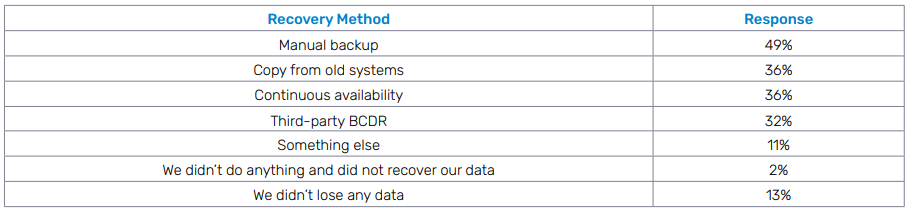
MSPs have a golden opportunity to expand revenue and help their customers reduce expensive downtime with solutions like BCDR, Managed SOC and incident response planning. About 49% of survey respondents said that their organizations relied on manual backup to recover data in their last cybersecurity incident (see Figure 4). That means that half of the businesses we surveyed need to upgrade to cloud backup and learn the benefits of BCDR — a big opportunity score for MSPs.
Downtime and the related cost may not be something that clients are considering when they’re making a cybersecurity-related cost- benefit analysis, However, it’s something an MSP needs to make sure their client is aware of in order to exemplify why taking steps to minimize downtime in the event of a successful cyberattack before it happens is a smart idea.
“When a business gets hit from the start to the point of remediation, we’re seeing numbers that indicate that the cost of downtime is roughly around 8k per hour,” cautioned McKie.
DePalma agrees, “The real question to ask is how long is it going to take you to recover from a cyberattack? The FBI says that 60% of businesses who get hit by a cyberattack go out of business within a year.”
5. Many SMBs need outside help to handle security.
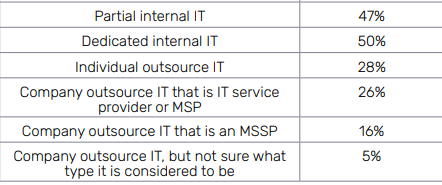
More than half of our survey respondents admitted that a successful phishing attack or even worse, a ransomware attack, would seriously wound their organization, with some saying that it could be a fatal blow. Many SMBs have that expectation because they’re not prepared to handle the fallout from a cyberattack. The cybersecurity skills shortage is only compounding their problems. That’s a big reason why a significant number of SMBs tend to rely on outsourced IT security. Businesses will continue to require expert help to maintain and enhance their security, and almost half of the IT professionals that we surveyed said that their organization relies on an MSP or MSSP to get the job done (see Figure 5).
SMB decision-makers aren’t necessarily informed about the need for a strong cybersecurity posture, creating hesitance when it comes to security spending. Business leaders who aren’t security-savvy may look at cybersecurity as an expensive budget-drainer instead of as a way to stave off an even bigger budget drain in the form of a cyberattack or other information security incident. However, MSPs benefit from changing that conversation by showing how security solutions not only prevent costly cyberattacks but also improve efficiency, saving payroll dollars.
“There’s still a lot of resistance from SMB leaders about spending on security,” says McKie. “A lot of that is due to the belief that security is an inhibitor or just a cost center. That’s one of the areas where we have to turn that story around to say no, security is actually going to save you money, it’s going to make you more efficient, more effective.”
Learn more about the mindset, motivation and challenges of SMB security decision-makers by reading the Datto SMB Cybersecurity for SMBs Report, available now, or watch the webinar Cybersecurity Roundtable Series: Key Insights iInto SMB’s Security Needs for MSPs webinar.